The World-Class Industrial
Cyber Security Roadmap
Services
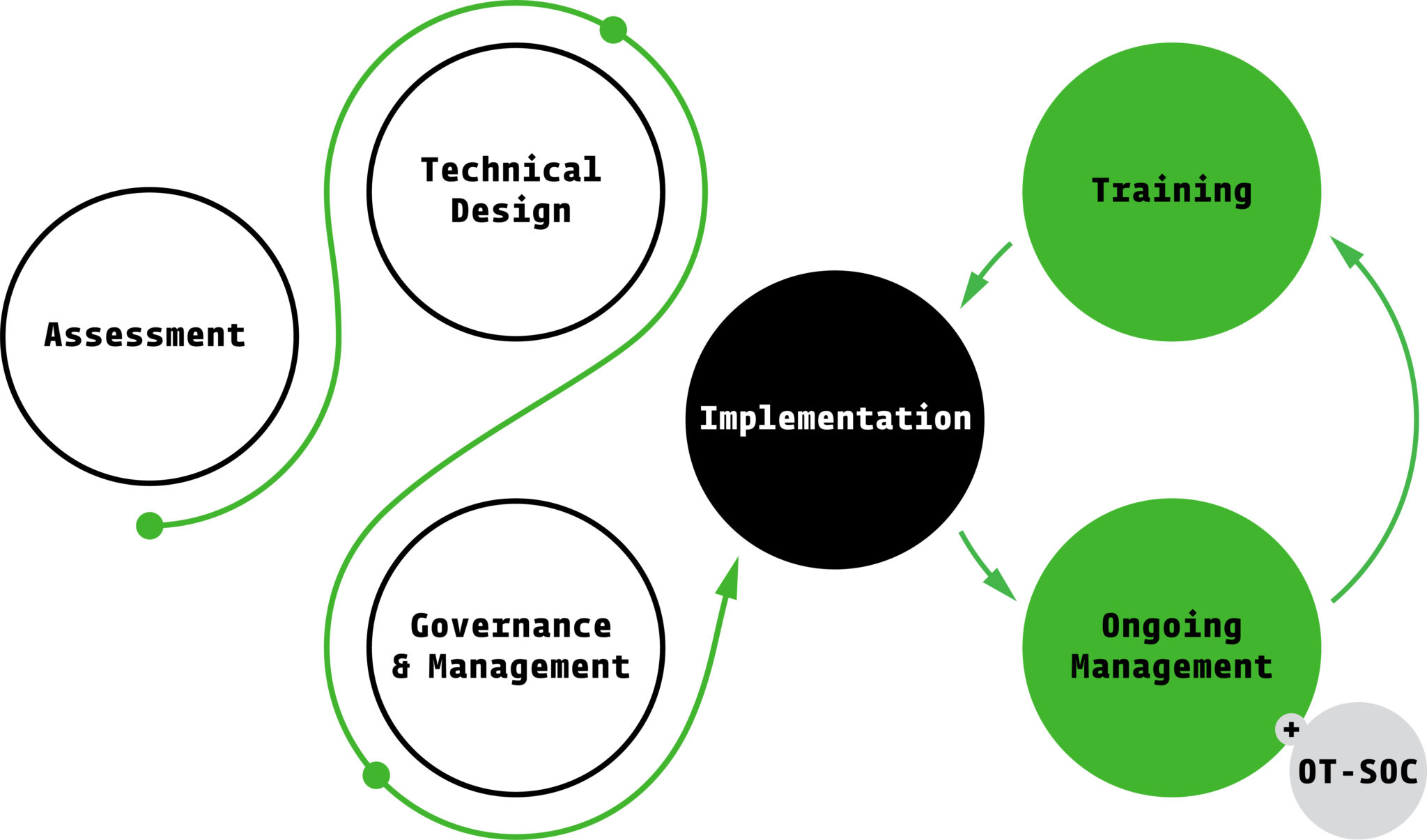
Our World-Class Industrial Cyber Security Roadmap
lays out a step-by-step plan; from assessing risks
to designing, implementing, and managing security
long-term. It’s built to cut through the
complexity, reduce risk, and help businesses stay
secure without disrupting operations.
- Comprehensive visibility of assets so you can prioritise what matters most.
- Identification of vulnerabilities & weaknesses helping you build a stronger defence.
- Detailed understanding of risk position & potential exploitability, aligning effort with actual exposure / avoiding wasted resources on low-risk areas.
- Insights into compliance obligations and steps towards achieving world-class industrial cyber security, giving stakeholders confidence in your program.
- A holistic security view that protects all business operations, reducing fragmentation and silos across your teams.
- Reduced attack surface and minimised risk safeguarding core systems from disruption.
- Understanding of control depth on every system across the OT environment, ensuring consistent protection across assets.
- A risk-based, methodical OT security design ready for implementation, so you can act with confidence, not guesswork.
- Provides standardisation of procedures and processes to manage and operate your OT systems security.
- Enhanced security posture, positioning you as a trusted operator.
- Capability to test and audit control effectiveness, reducing the risk of false security.
- Establishment of a common security language across the organisation, aligning teams around shared goals.
- Assurance of regulatory compliance, enabling smooth audits and reporting.
- Assurance and validation of security control effectiveness via building confidence in real-world performance.
- Tangible and measurable security outcomes proving ROI and program value / enabling clear reporting to the board.
- Sustained peace of mind with ongoing OT security capabilities reducing stress and operational risk.
- The comfort and support from an elite industrial cyber team aiding in your organisations detection and response capabilities.
-
Benefit from uninterrupted operations and maximised production uptime, with your OT network continuously protected 24/7 from cyber threats.
-
Gain peace of mind knowing your organisation consistently meets legislative and regulatory requirements through the application of industry-recognised standards and frameworks.
-
Enjoy the confidence that comes with a customised OT cyber security program, regularly audited and reviewed to ensure controls remain effective, providing clear, actionable insights for both security teams and management.
- Creation of resilient and vigilant staff, turning your team into the first line of defence.
- Cultivation of a security-aware workforce creating a culture of accountability.
- Achievement of better industrial security outcomes through educated personnel, reducing dependency on external responses.
SIS conducted a risk assessment of our operational technology environment and we were very impressed with their approach, methodology, execution, and delivery. They are adaptable, technically astute, and demonstrated a strong ability to fully understand business requirements specific to the oil and gas sector.
PMO and GRC ConsultantOil and Gas
The project provided our organisation with a clear view of our cyber security maturity and highlighted the range of threats that could impact our systems at any time.
As a result of the assessment, several mitigation steps have already been implemented based on SIS’ key recommendations.
SCADA and EMS ProgrammerEnergy Interconnection
SIS delivered an Information Security Management System framework that ensured governance was appropriately embedded across ICT operations, including business critical control systems. This significantly strengthened our audit compliance posture against recognised industry standards.
Chief Information OfficerWater Utility
SIS effectively identified the required security controls to ensure essential services such as patching, configuration management, data backup, and secure remote access were available across both IT and OT environments for our new ADMS platform.
Their familiarity with OT security is exceptional.
ADMS Project ManagerElectricity Distribution
SIS’ tailored methodology for control systems testing demonstrated a high level of specialist expertise in this domain.
They also showed strong flexibility in accommodating changing schedules and efficiently mobilising resources to meet critical production deadlines during a major network management system upgrade.
OT Security LeadEnergy Infrastructure
SIS consultants applied a professional and structured approach to a complex OT enablement scenario. This resulted in comprehensive designs covering key functional and non functional requirements, while also identifying security risks and the supporting process framework.
SIS is best in class for IT and OT integration work.
Technology Program ManagerMining and Resources
SIS’ level of expertise in operational technology security is outstanding.
Senior Technology LeaderRail and Freight Transport
See how
your organisation
stacks up against
the benchmark
Put your organisation
to the test with the
SIS Industrial Cyber
Security Assessment
Scorecard.